Security
-
CISA confirms exploitation of 3 more Cisco networking device vulnerabilities
Cisco revealed six critical flaws in widely used products in February. The government has now seen evidence that hackers are abusing four of them.
By Eric Geller • April 21, 2026 -
Big banks seek to ease security worries as AI push accelerates
“AI is our friend, OK?” said Morgan Stanley CEO Ted Pick during the bank’s earnings call as the industry grapples with its disruptive potential.
By Makenzie Holland • April 17, 2026 -
CISOs see gaps in their incident response playbooks
Senior-level security leaders fear they are not prepared to respond to the next cyberattack, a survey by Sygnia reveals.
By David Jones • April 17, 2026 -
Sponsored by Palo Alto Networks
Why securing GenAI use starts in the browser
As GenAI adoption surges, security risks grow in the browser—where 80% of work happens. Learn how secure browsers like Prisma Browser close the gap.
April 13, 2026 -
Sponsored by Palo Alto Networks
Future-proof your security and reduce quantum risk with cryptographic agility
Cryptographic agility is emerging as a key strategy for resilient encryption against quantum computing risks in an evolving security landscape.
April 6, 2026 -
Sponsored by Palo Alto Networks
Building organizational readiness for post-quantum cryptography
91% of organizations lack a plan for post-quantum cryptography as the quantum era approaches.
March 30, 2026 -
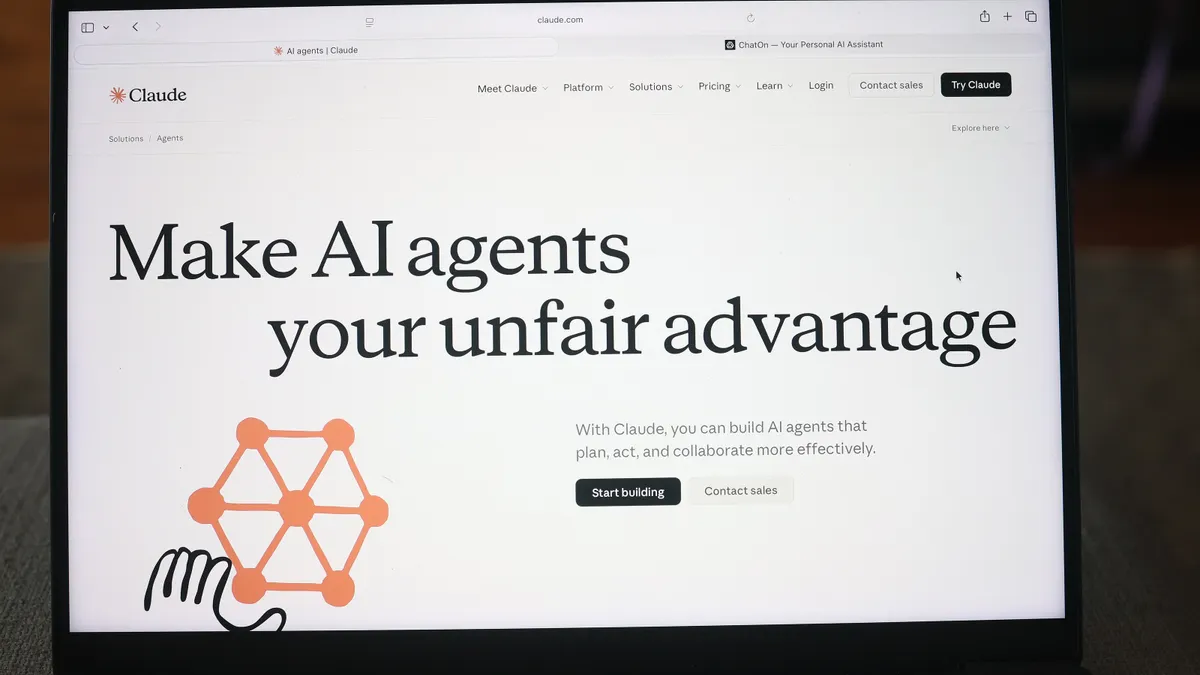
Databricks unveils agentic security platform to fend-off AI threats
The data and AI provider's launch of Lakewatch comes amid rising concerns over cyberattacks fueled by agentic AI.
By Scarlett Evans • March 26, 2026 -
Companies know AI is essential for cyber defense but aren’t yet seeing returns
The maturity of organizations’ AI oversight also varies significantly, according to a new EY survey of cybersecurity leaders.
By Eric Geller • March 20, 2026 -
CISA urges organizations to harden endpoint security following Stryker attack
The agency is coordinating with the FBI and other agencies amid concerns about additional threat activity involving Microsoft Intune.
By David Jones • March 19, 2026 -
IT values AI in security, but human oversight remains key
Integration issues and governance concerns limit AI’s effectiveness in security workflows despite widespread adoption, according to a Crogl report.
By Makenzie Holland • March 18, 2026 -
Even primitive AI-coded malware helps hackers move faster, thwart attribution
IBM researchers discovered an autonomously coded backdoor that they called unsophisticated but nonetheless ominous.
By Eric Geller • March 16, 2026 -
Trump’s new cybersecurity strategy makes promises but lacks details
In a document released Friday, the administration vowed to increase the government’s use of AI for rapid cyber defense.
By Eric Geller • March 10, 2026 -
Shadow AI rises as leaders choose speed over governance
Most AI initiatives at a department level are going live without formal company oversight even as risks mount, according to an EY survey.
By Scarlett Evans • March 9, 2026 -
AI’s ‘connective tissue’ is woefully insecure, Cisco warns
In a new report, the company also said businesses should beware of the “SolarWinds of AI.”
By Eric Geller • Feb. 20, 2026 -
Ransomware attacks increase against IT and food sectors
Social engineering and zero-day vulnerability weaponization are getting faster and easier, two information sharing and analysis centers said in new reports.
By Eric Geller • Feb. 13, 2026 -
Autonomous attacks ushered cybercrime into AI era in 2025
Malwarebytes urged companies to adopt continuous monitoring and lock down identity systems as AI models get better at orchestrating intrusions.
By Eric Geller • Feb. 4, 2026 -
AI tools break quickly, underscoring need for governance
Security firm Zscaler said it identified severe vulnerabilities in every enterprise tool it tested — sometimes on its first prompt.
By Eric Geller • Jan. 28, 2026 -
EU wants Google to share its data in compliance with legislation
The European Commission directed Google to grant third-party providers the same data access as Gemini to comply with the Digital Markets Act.
By Makenzie Holland • Jan. 27, 2026 -
Coca-Cola taps first-ever chief digital officer
The beverage maker picked Sedef Salingan Sahin to serve in the newly created CDO role citing a pressing need to accelerate tech adoption.
By Roberto Torres • Jan. 14, 2026 -
Nationwide Financial taps tech veteran as CTO
Misty Kuamoo will be responsible for technology products supporting the insurer’s financial services businesses, the company announced Friday.
By Makenzie Holland • Jan. 12, 2026 -
How CIOs can brace for AI-fueled cyberthreats
Executives are carefully tracking the rise in AI use for cyberthreats, bolstering basic preparedness tactics and increasing cyber spend in response.
By Jen A. Miller • Jan. 7, 2026 -

 R. Eskalis/NIST. Retrieved from NIST.
R. Eskalis/NIST. Retrieved from NIST.
NIST asks public for help securing AI agents
The agency is interested in case studies showing how best to protect agents from hackers.
By Eric Geller • Jan. 7, 2026 -
Cyber risks grow as manufacturers turn to AI and cloud systems
Manufacturing has been the most-attacked sector for four years straight, according to a recent IBM report. Experts weigh in on how to balance the costs of security infrastructure with the rapid pace of technological advancement.
By Sakshi Udavant • Jan. 5, 2026 -
ServiceNow to buy Armis for $7.75B
The combination yields a major player in cyber-physical security and exposure management.
By David Jones • Dec. 23, 2025 -
New York mandates AI model safety requirements
Despite President Donald Trump’s executive order challenging states' authority, New York Governor Kathy Hochul signed AI safety legislation into law.
By Makenzie Holland • Dec. 22, 2025